COMPONENTS OF A NETWORK
THERE ARE 6 MAIN COMPONENTS OF A NETWORK
The Router
For most home users, they may want to set-up a LAN or WLAN and connect all computers to the Internet without having to pay a full broadband subscription service to their ISP for each computer on the network. In many instances, an ISP will allow you to use a router and connect multiple computers to a single Internet connection and pay a nominal fee for each additional computer sharing the connection. This is when home users will want to look at smaller routers, often called broadband routers that enable two or more computers to share an Internet connection.
Switch
In networks, a device that filters and forwards packets between LAN segments. Switches operate at the data link layer and sometimes the network layer of the OSI Reference Model and therefore support any packet protocol. LANs that use switches to join segments are called switched LANs or, in the case of Ethernet networks, switched Ethernet LANs.
A small lever or button. The switches on the back of printers and on expansion boards are called DIP switches. A switch that has just two positions is called a toggle switch.
Another word for option or parameter -- a symbol that you add to a command to modify the command's behavior.
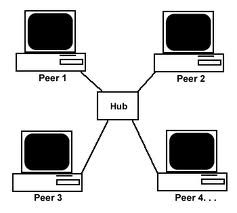
Hub
A hub is used in a wired network to connect Ethernet cables from a number of devices together. The hub allows each device to talk to the others. Hubs aren't used in networks with only wireless connections, since network devices such as routers and adapters communicate directly with one another.
Hubs are such simple devices — they require no configuration, and have no manuals — that their function is now included in other devices such as routers and modems.
If you have several computers and need to network them, you do not have to spend a lot of money to accomplish your goal. Network hubs are inexpensive and provide stable network connectivity for small networks. A network hub is a passive device in that it broadcasts packets received from one computer to all other attached devices. For this reason, hub-based networks should not connect more than ten computers.
Server
You call the server by what task it needs to do. For example
Print server: this is connected to the network printers and acts as the go-between for your computer and the printer when you send a document to print. The print server handles the task for you, leaving you free to get on with something else. If a job seems to be taking a long time, then you can normally click on your printer icon in the task bar to have a look at the 'print queue' to see what is holding it up.
File server: This handles the sharing and storing of files on the network. You will normally see 'Network Drives' in Windows Explorer as well as your local 'C' drive. These drives are part of the file server. You can have many file servers on a network.
Web Server: This handles the delivery of web pages and files linked to those web pages. A web server can sit on an Intranet so it remains private to those users. Or it can be connected to the Internet, in which case it will be handling one or more domain names
client
NIC
A network interface card, or NIC, is an installed hardware device that enables computer networking. In networking, one computer is communicates with another, sending and receiving information via a shared channel designed for such a purpose. The most obvious example of this practice is the Internet and those who access it to present and obtain information. Yet there are many other networks, a number of ways to access them, and considerable methods for transferring data across them. For this reason, NICs are not only used to enable networking, they are also used to support the countless networking preferences maintained by computer users.
peer to peer network
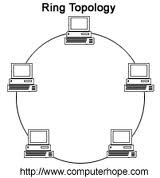
Ring network
-Advantages
Data is quickly transferred without a ‘bottle neck’. (very fast, all data traffic is in the same direction)
The transmission of data is relatively simple as packets travel in one direction only.
Adding additional nodes has very little impact on bandwidth
It prevents network collisions because of the media access method or architecture required.
-Disadvantages
Data packets must pass through every computer between the sender and recipient therefore this makes it slower.
If any of the nodes fail then the ring is broken and data cannot be transmitted successfully.
It is difficult to troubleshoot the ring.
Because all stations are wired together, to add a station you must shut down the network temporarily.
In order for all computers to communicate with each other, all computers must be turned on.
Total dependence upon the one cable
A ring network is a local area network (LAN) in which the nodes (workstations or other devices) are connected in a closed loop configuration. Adjacent pairs of nodes are directly connected. Other pairs of nodes are indirectly connected, the data passing through one or more intermediate nodes.
Star network
-Advantages
Good performance
easy to set up and to expand. Any non-centralised failure will have very little effect on the network, whereas on a ring network it would all fail with one fault
-Disadvantages
Expensive to install
Extra hardware required
In a star network each device on the network has its own cable that connects to a switch or hub. A hub sends every packet of data to every device, whereas a switch only sends a packet of data to the destination device.
Bus network
-Advantages
Easy to implement and extend
Well suited for temporary networks (quick setup)
Initially less expensive than other topologies
Cheap
-Disadvantages
Difficult to administer/troubleshoot.
Limited cable length and number of stations.
If there is a problem with the cable, the entire network goes down.
Maintenance costs may be higher in the long run.
Performance degrades as additional computers are added or on heavy traffic.
Low security (all computers on the bus can see all data transmissions).
One virus in the network will affect all of them (but not as badly as a star or ring network).
Proper termination is required.(loop must be in closed path).
If one node fails, the whole network will shut down.
If many computers are attached, the amount of data flowing causes the network to slow down.
this is one method of connecting computers together and it is the easiest. a single cable joins all the work stations, printer, file server and other components together. at the end of the bus is a 'terminator' which prevents signals from bouncing back and forth, other wise known a 'echoes'.
Ring network
if there was one break in the line then the whole network will go down, traffic also cant take the most efficient route.
bus network
only one computer can use the bus at once, this means only one can communicate at one time. the others have to wait until the bus is free to send their data, this makes it slow. if a computer connected to the bus breaks down, then the network still runs but if the central bus breaks down then so does the whole network.
Star network
if the main server fails the whole network goes down.
LAN
WAN
difference between LAN and WAN
The other difference between LAN and WAN, is the speed of the network. The maximum speed of a LAN can be 1000 megabits per second, while the speed of a WAN can go up to 150 megabits per second. This means the speed of a WAN, is one-tenth of the speed of a LAN. A WAN is usually slower because it has lower bandwidth.
Computers in a LAN can share a printer, if they are all in the same LAN. On the other hand, a WAN cannot share a printer, so a computer in one country cannot use a printer in another country. A LAN does not need a dedicated computer to direct traffic to and from the Internet, unlike a WAN that needs a special-purpose computer, whose only purpose is to send and receive data from the Internet.
• Disaster recovery procedures
from a virus, hacking or simply a fire or flood or other act of nature- there may come a time when you will experience a catastrophic loss of computer data. You may lose Data due to- hacker attacks
- computer viruses
- electric power failures
- underground cable cuts or failures
- fire, flood, earthquake, and other natural disasters at a facility
- mistakes in system administration
there are many ways that you can save/ retrieve your data. Traditional backup strategies, for example, archive copies of critical data at a given point in time so that they can be restored later if needed. virus scanning software can be used to get rid of data wiping virus’.
- Hackers
- Unauthorised access to files/folders by employees
Matt’s section - Hardware Failures & Software Failures
Hardware Failure - Failure of main systems components such as CPUs and memory; or peripherals such as disks, disk con ers, network cards; or auxiliary equipment such as power modules and fans; or network equipment such as switches, hubs, cables, etc., can be the causes of hardware failures.
Software Failures - The possibilities of failure of software mostly depends upon the type of software used. One of the main causes for software failure is applying a patch. Sometimes, if a patch does not match the type of implementation, then the application software may start to behave in a strange way, bringing down the application and reversing the changes, if possible. Sometimes, an upgrade may also cause a problem. The main problem with upgrades will be performance related or the misbehaving of any third party products, which depend upon those upgrade
Cameron’s Section
If your computer is under warranty, you want to have the warranty information in your security box with other important documents. This allows you to grab the information when you get ready to evacuate. In some cases, companies will replace a computer that is damaged due to a natural disaster. You can also purchase replacement warranties that will replace the computer no matter what happens to it. While you may not plan on losing your computer, that doesn’t mean it won’t happen. You need to backup your important photos and financial files to a cloud storage system. This will allow you to access the files no matter where you are or whether or not your computer still works. This can save you a lot of time and heartache. With a backups they are easy to make and really good when you have lots of important information that can be devastating if you lose it. If there is a flood all of your possessions will be lost and a backup can restore all your information back on to a different computer.
Callums section
Bomb
A logic bomb is a piece of code intentionally inserted into a software system that will set off a malicious function when specified conditions are met. For example, a programmer may hide a piece of code that starts deleting files (such as a salary database trigger), should they ever be terminated from the company.
Software that is inherently malicious, such as viruses and worms, often contain logic bombs that execute a certain payload at a pre-defined time or when some other condition is met. This technique can be used by a virus or worm to gain momentum and spread before being noticed. Some viruses attack their host systems on specific dates, such as Friday the 13th or April Fool's Day. Trojans that activate on certain dates are often called "time bombs".
To be considered a logic bomb, the payload should be unwanted and unknown to the user of the software. As an example, trial programs with code that disables certain functionality after a set time are not normally regarded as logic bombs.
Access rights Dylan Evans (Fridylol)
Access rights are the rights that are set out by the administrator on the network, that state what documents and files each person can access. For instance, you may have a personal folder in which you have the right to open, read, write, create and delete files. Parts of the network may have files that you are only able to read and not edit and there may be parts of the network you can’t access at all. In which case a message will often pop up to inform you "You do not have sufficient access rights" or something similar.You may be able to access certain areas because you are part of a group, for example a student group. If you are part of a group on the network, you will have the same access rights as everyone else in the group.
Acceptable use policy
An acceptable use policy is a set of rules applied by the owner/manager of a network, website or large computer system that restrict the ways in which the network, website or system may be used. AUP documents are written for corporations, businesses, universities, schools, internet service providers, and website owners often to reduce the potential for legal action that may be taken by a user, and often with little prospect of enforcement.
Acceptable Use Policies are an integral part of the framework of information security policies; it is often common practice to ask new members of an organization to sign an AUP before they are given access to its information systems. For this reason, an AUP must be concise and clear, while at the same time covering the most important points about what users are, and are not, allowed to do with the IT systems of an organization. It should refer users to the more comprehensive security policy where relevant. It should also, and very notably, define what sanctions will be applied if a user breaks the AUP. Compliance with this policy should, as usual, be measured by regular audits.
Firewall KYNE
Firewalls are commonly used as a source of protection for keeping networks safe and secure. They can either be Hardware based or Software based. However, its primary objective is to control the incoming and outgoing network traffic, this is generally done by the software analyzing the data packets then determining whether or not it should be authorized to pass through the network into the computer. If the data packet is declined then it is just forgot about by the Firewall, but if it is accepted then once in the computer the packet will then do what is was programmed for.
Password by Ben A
Passwords are used throughout most computer systems to protect data on computers even computers without precious data files normally have passwords just for a sense of security. Passwords now when created have strength meters to check how strong it is against hackers. Sometimes it won’t even allow weak passwords because it is such a danger. Passwords are classified in strength by the amount of letters numbers and cases and symbols for example an extremely strong password could be: Fa4%0Op$; this is because it is quite long, uses all cases some symbols and some numbers. However weak passwords would use one case or just numbers or just symbols.
Passwords are like locks they will only let somebody into a computer system if they have the code. They can also be used to lock files and other things such like. If a hacker should try attacking the system and guess the password; a good password security system will give a number of tries to get into the computer then the computer will lock itself and you will have to wait a predetermined time until you can try again.
Passwords are used throughout most computer systems to protect data on computers even computers without precious data files normally have passwords just for a sense of security. Passwords now when created have strength meters to check how strong it is against hackers. Sometimes it won’t even allow weak passwords because it is such a danger. Passwords are classified in strength by the amount of letters numbers and cases and symbols for example an extremely strong password could be: Fa4%0Op$; this is because it is quite long, uses all cases some symbols and some numbers. However weak passwords would use one case or just numbers or just symbols.
Passwords are like locks they will only let somebody into a computer system if they have the code. They can also be used to lock files and other things such like. If a hacker should try attacking the system and guess the password; a good password security system will give a number of tries to get into the computer then the computer will lock itself an you will have to wait a predetermined time until you can try again.
- Alex’s Section - Firewall software
- Is used to keep a network safe and secure.
- Its primary objective is to control the incoming and outcoming traffic and analysing the data packets and determining whether they should be allowed in or not.
- We need to use firewalls because they are one of the best ways to protect computers, if we didn’t have them then we would be prne all the time to viruses and other things that can harm your computer.
- in a situation where you are using a computer with important info on it, if you were to be hit by a virus all of the important info you were using will be lost and you will be annoyed. this was all because of the fact that he/she had no firewall. this is why they are so important.